What Is a Hash?
Ok, firstly alot of you still believe that hashes can be "", this is a common
misconception because hashes are generated by One Way Cryptographic Hash Algorithms these means the algorithm
that created them CAN NOT be reversed to determine the plain text password.
These one way functions are used by computers to prevent storing passwords in plain text in memory,
instead when a password is entered (for example at a log in screen) a one way hash algorithm is applied to the supplied password
and then the hashed output is compared to the hash for that user, stored in memory.
If the two hashes match, the passwords are the same and the user is authenticated,
if the two hashes are not the same the passwords do not match and the user is denied access.
Types Of Hashes And How To Identify Them
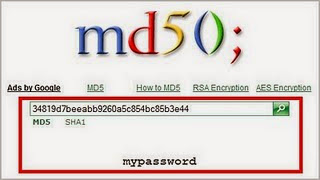
MD5 - The most common hash you will come across in the wild is an MD5 hash
(Message-Digest algorithm).
These hashes are easily identified by the following factors:
- They are always 32 characters in length (128 Bits)
- They are always hexadecimal (Only use characters 0-9 and A-F)
Example - f5d1278e8109edd94e1e4197e04873b9
If the hash breaks one of these rules - IT IS NOT MD5.
SHA1 - Still used frequently on the internet and is one of a large family of Secure Hash Algorithms.
These hashes are easily identified by the following factors:
- They are always 40 Characters in length (160 bits)
- They are always hexadecimal (Only use characters 0-9 and A-F)
Example - ab4d8d2a5f480a137067da17100271cd176607a1
If the hash breaks one of these rules - IT IS NOT SHA1.
MySQL < 4.1 - These aren't used very often but still come up on very often because people have no idea what to do with them, they are used in older versions of Mysql. These hashes are easily identified by the following factors - They are always 16 Characters in length (64 bits) - They are always hexadecimal (Only use characters 0-9 and A-F) If the hash breaks one of these rules - IT IS NOT MYSQL < 4.1.
Example - 606727496645bcba
MYSQL5 - Used in newer versions of MYSQL to store database user passwords.
These hashes are easily identified by the following factors
- They are always 41 characters in length
- They are always capitalized
- They always begin with an asterisk
If the hash breaks one of these rules - IT IS NOT MYSQL5.
Example - *C8EB599B8E8EE7BE9F1A5691B7BC9ECCB8DE1C75
MD5(Wordpress) - Used in word press driven sites, one of the most commonly confused hashes by everyone
These Hashes are easily identified by the following factors
- They always start with $P$
- They are always variable case alpha numeric (0-9 A-Z a-z)
- The are always 34 characters long
If the hash breaks one of these rules - IT IS NOT MD5(Wordpress).
Example - $P$9QGUsR07ob2qNMbmSCRh3Moi6ehJZR1
MD5(phpBB3) - Used in PHPBB forums, another commonly miss identified hash, especially amongst skids.
These Hashes are easily identified by the following factors
- They always start with $H$
- They are always variable case alpha numeric (0-9 A-Z a-z)
- The are always 34 characters long
If the hash breaks one of these rules - IT IS NOT MD5(PhpBB).
Example - $H$9xAbu5SruQM5WvBldAnS46kQMEw2EQ0
SALTS:-
Ok now there is ALOT of confusion around salts , so im going to try and quickly clean this up - the most commonly salted hash is MD5 because it is cryptographically weak and easy to crack. So a salt gets added to the password before hashing to increase the parity. For example MD5($password.$salt).
Salted MD5 - Used in a large amount of applications to increase hash parity and to increase the time it takes to crack.
These Hashes are easily identified by the following factors
- They consist of two blocks connected by a colon, the first is the hash the second is the salt.
- The first part of the salted hash is hexadecimal, the second is variable case alphanumeric.
- They first part will always be 32 characters long
- The second part can be any length.
If the hash breaks one of these rules - IT IS NOT A SALTED MD5.
Example - 49adee90123f8c77d9020bba968c34dd:PS2en
Warning - in some cases the salt can contain symbols (but this is rare)
NOTE - You need both the salt AND the hash to decrypt a salted md5.
How To Crack Hashes
MD5 - MD5 hashes are easily broken in the present day due to the prevalence of online MD5 crackers such as www.hashchecker.de.
However if you cant crack your hash online then you will need to use a tool such as John The Ripper or more advanced hash crackers
such as Password Pro or HashCat.
No comments:
Post a Comment